-

Email phishing using domain spoofing
In January 2023, one of our clients reported that a scammer had registered a similar looking domain as that of our client and was using this spoofed domain to send fake invoices to our client’s clients with the scammer’s bank account details. As an example assume client’s website had the word ‘group’ in it like…
-

Junk the old methods, adopt easier & modern password practices
Change passwords frequently Don’t share your passwords with anyone Don’t write it down Add symbols and upper lower plus alphabets and numbers Sounds familiar? Security experts feel the world is very different now and while we should still stick to the general recommendations for passwords, there are some things we can let go of. Change…
-
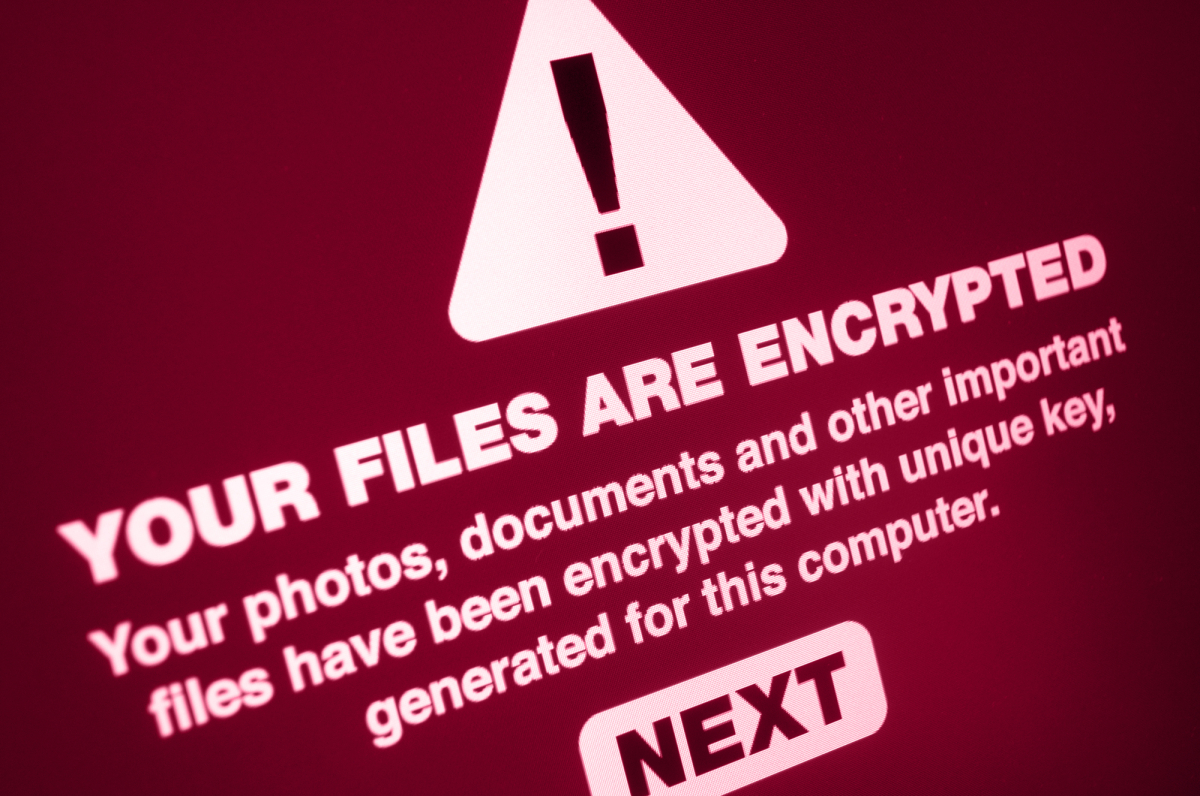
Ransomware
Ransomware is a malware that will either disable access to your data or threaten to publish it. They hold you at ransom unless money is paid off. The data is encrypted using a key the hacker possesses. Without this the data cannot be decrypted. Ransomware can be downloaded onto systems when unwitting users visit malicious…
-

Potential power blackout in the UK this winter
The UK is bracing itself for potential power cuts amidst the energy crisis. The boss of the National Grid John Pettigrew admitted that it’s possible for rolling power cuts (blackouts) as energy supplies run low. Our suggestions below are just a few tips for being better prepared. No way are suggesting that a blackout will…
-

Incident management and reporting template
For business continuity every organization should have 2 processes/documents/plans, disaster recovery and incident management. Incident management is exactly what the term implies, managing an incident that could lead to loss or disruption of an organizations processes. Even a small company should have a basic incident management plan which is well communicated with all team members…
-

Lessons learnt from “Uber Files”
“Uber Files”: A leak of 1,24,000 internal Uber documents spanning a period between 2013, and 2017. This leak has been damaging to Uber and you can read details on this link https://www.icij.org/investigations/uber-files/frequently-asked-questions-about-the-uber-files/ Few key lessons to be learnt are, Have an incident management team ready which includes top executives and technical and key managers for…
-

Good bye Debian 9, welcome 11
Around 15 years back when we decided to start a server administration division, we were wondering which Linux based OS to use. We finally decided on Debian after evaluating many different Linux distributions. Some advantages of Debian – Debian is free and open source software and will always be 100% free. – Debian is stable…
-

SaaS misconfiguration a major finding
The “2022 SaaS Security Survey Report” is out and the key findings are around SaaS (Software as a Service) misconfiguration, which is leading to security incidents. The causes for these are multiple including, lack of visibility, too many departments with access, lower investment in security tools and staff. Of those who took part in the…
-

Biggest DDoS attack to hit a Crypto Platform
Cloudflare has said that they received one of the DDoS attacks with 15.3 million requests.DDoS Attack means “Distributed Denial-of-Service (DDoS) Attack” and it is a cybercrime in which the attacker floods a server with internet traffic to prevent users from accessing connected online services and sites. Key points to note. The attack lasted just 15…