-

FAQ for European Accessibility Act (EAA) enforced on 28th June 2025 and WCAG 2.1 Level AA
Note this is a general document for reference and we ask you to refer to your legal department for the correct scope and coverage of the law.
-

How Secure Is Your Website? 10 Critical Questions Every Site Owner Must Answer
Why you need to ask yourself these questions? In today’s digital landscape, your website is more than just a business card, it’s often your most public-facing and vulnerable asset. Whether you’re running an e-commerce store, a corporate site, or a personal blog, attackers are constantly scanning the web for weak points to exploit. From stolen…
-

Skype is Shutting Down – Transitioning to Google Chat & Meet
As you may have heard, Microsoft is officially shutting down Skype on 5th May 2025. To ensure a smooth transition, we are moving to Google Workspace Chat and Google Meet as our official communication platforms for chat and video calls. For those clients and partners who require Microsoft Teams, we will continue to offer support…
-

How to Protect Your Business from Email Scams
Real-World Email Scam Incident A few days ago, one of our clients received an email from Jonny, appearing as a continuation of an existing thread of correspondence. However, it was actually a scammer impersonating Jonny, attempting to change our bank details to divert a deposit to their own account. How the Scam Worked The scammer…
-

Cryptographic failures (Sensitive Data Exposure)
Cryptographic failures refer to weaknesses, vulnerabilities, or mistakes in the implementation, configuration, or use of cryptographic systems that compromise the security and confidentiality of sensitive data. These failures can result in unauthorized access, data breaches, or a loss of trust in the system. Cryptographic failures often occur when cryptography is not applied correctly, is outdated,…
-

Holiday Shopping Security: Protecting Yourself from Seasonal Scams
The holiday season brings joy, celebrations, and a surge in shopping activity. Unfortunately, it also provides an opportunity for cybercriminals and fraudsters to exploit the festive rush. Whether you’re shopping online or in-store, being aware of potential threats and taking proactive steps can protect you from becoming a victim of holiday scams. Here’s how you…
-
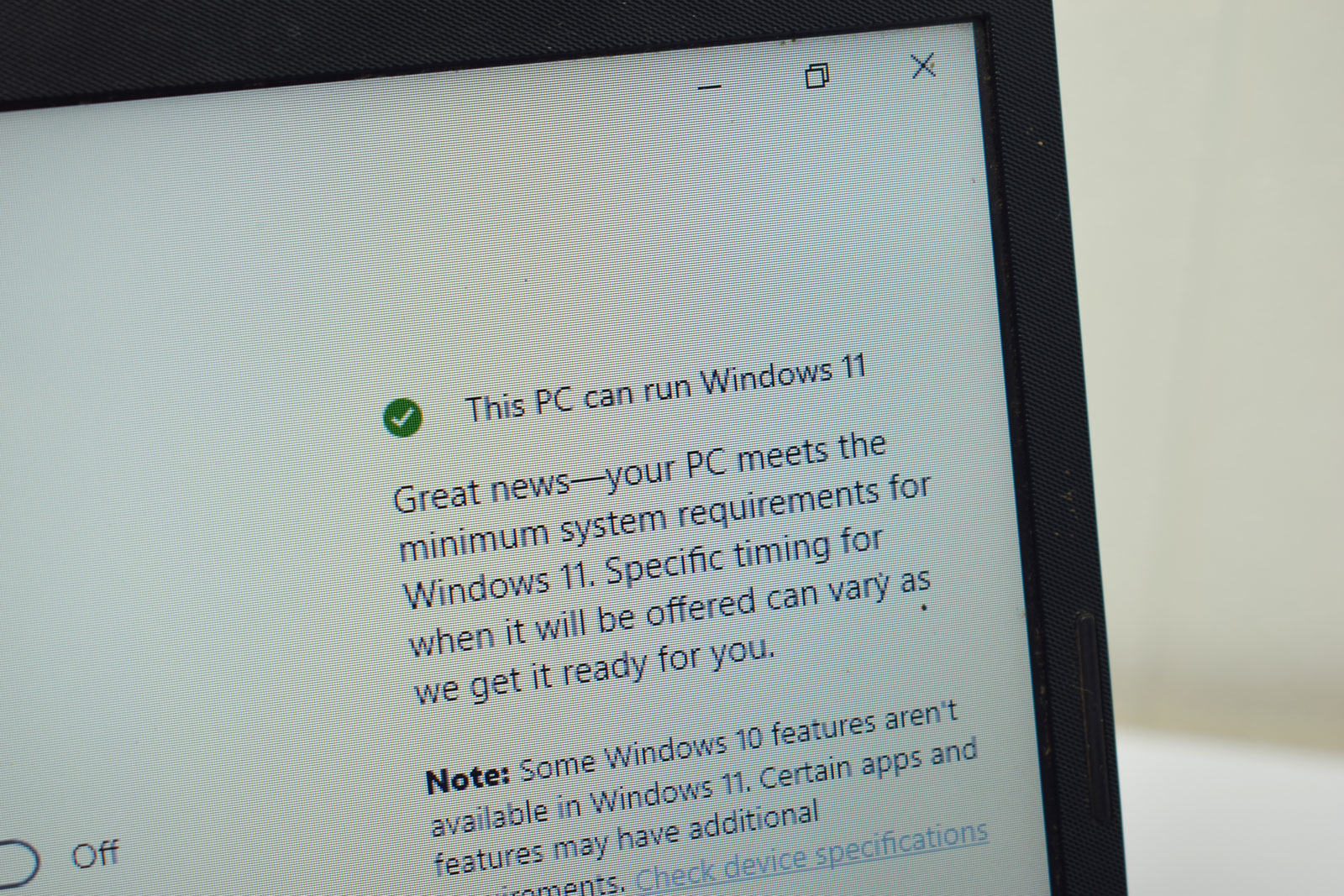
Windows 10 End of Life and the Challenges of Upgrading to Windows 11: What Businesses and Consumers Need to Know
Windows 10 will officially reach its end of life (EOL) on October 14, 2025. After this date, Microsoft will no longer provide technical support or security updates, leaving Windows 10 systems vulnerable to security threats, malware, and other issues. While Windows 10 will still function after the EOL date, continuing to use it poses serious…
-
Hidden Risks of Smart Devices: Why Your Home Automation Could Be a Security Nightmare
In recent years, there has been a surge in “smart” versions of traditional home devices. Devices once purely mechanical or locally controlled are now connected to the network/internet, often relying on cloud-based applications for enhanced functionality. From locks and security cameras to doorbells and home appliances, these connected devices aim to make life easier and…
-

Common scams in 2024
Forbes has listed the common scams currently affecting users and establishments Ticket scams: Selling fake tickets to events.Impersonation scams: Pose as an authoritative figure to transfer funds or get information.Loan fee fraud: Charging a fee for fake loans.Authorised push payment scams: Getting users to transfer moneyParcel delivery scams: Additional fee for delivery of a parcelIdentity…