Strengthening Web Application Security: A 9-Day Pentest Success Story
At sapna security, we recently got a go ahead with a web application to conduct a comprehensive penetration test (pentest) aimed at uncovering security weaknesses.
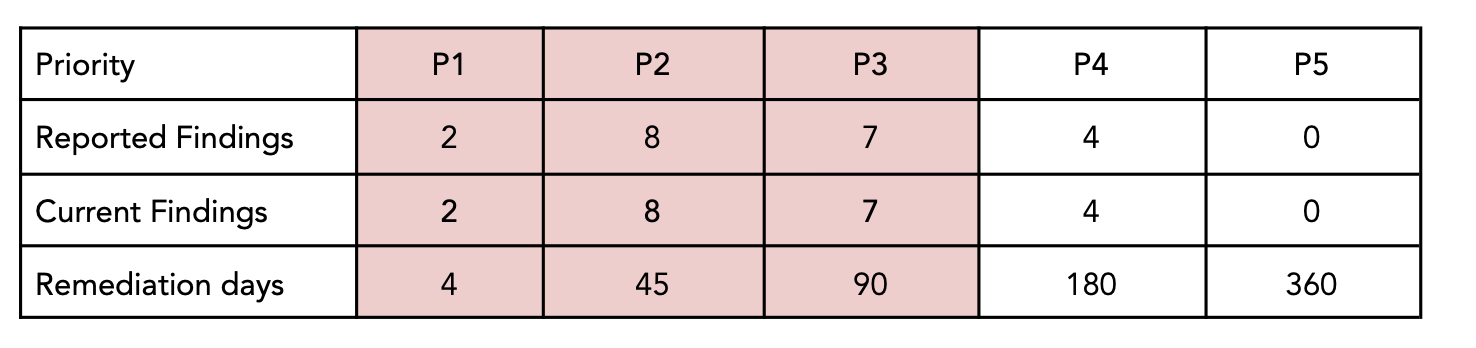
The client provided us with a dedicated test environment, and over the course of 9 days, our security team performed a deep-dive application assessment, resulting in a detailed report with 21 vulnerabilities, including 2 critical (P1) issues.
Our Testing Approach
We approach every pentest with a combination of manual analysis, automated scanning, and threat modeling. For this assessment, we focused on key areas critical to modern web applications:
1. Injection Attacks (SQL, OS command injection)
2. Authentication & Session Management
3. Cross-Site Scripting (XSS)
4. Access Control & Authorization
5. Sensitive Data Exposure & Cryptography
6. CSRF (Cross-Site Request Forgery)
7. Unvalidated Redirects and Input Validation
8. Third-Party Components & Dependencies
Key Findings
Our findings were classified using our P1 (Critical) to P5 (Informational) scale:
2 Critical (P1)
– OS Command Injection
– SQL Injection
8 High (P2)
– Multiple Reflected XSS vulnerabilities
– Vulnerable outdated WordPress version
– Weak CORS configuration
– Non-expiring tokens in URLs
– Insufficient session timeout
– Broken Access Control
7 Medium (P3)
– Outdated PHP version
– Vulnerable WordPress plugin
– Vulnerable JavaScript dependencies
– Insecure file upload functionality
– Insecure design patterns
– Use of unmaintained third-party components
4 Low (P4)
– Missing security headers
– Weak password hashing
– Duplicate/Insecure Cache-Control headers
– Insufficient Access Control in WordPress
Each issue was accompanied by detailed technical evidence, proof-of-concept exploits, and actionable remediation guidance tailored to the client’s tech stack.
Collaboration and Remediation
Following our assessment, we held a comprehensive debriefing session with the client’s management and development teams. Together, we prioritized fixes, with critical P1 vulnerabilities addressed as the top priority. Work is now actively underway to strengthen the platform’s overall security posture.
Takeaway
This engagement highlights why regular pentesting is vital for any application handling personally identifiable information (PII) or sensitive data – from ecommerce websites to fintech, healthcare, and enterprise SaaS. Early identification and remediation of vulnerabilities not only reduce risk but also reinforce customer trust and regulatory compliance.
At sapna security, we’re committed to helping businesses across industries stay ahead of evolving threats.